Include custom attributes in cognito claims
Amazon Cognito ID Token includes standard user attributes (these things also known as JWT token claims), so they can be received in your lambda if you use some cognito authorizer or even could be read on frontend.
For example if you are using serverless framework, yaml config will look like:
functions:
simplefunction:
handler: simplefunction.main
events:
- http: post simplefunction/call
integration: lambda
authorizer:
arn: arn:aws:cognito-idp:us-east-1:xxxxx:userpool/us-east-1_xxxxxxxxxx
claims:
- email
- nickname
In node.js lambda map of attributes can be accessed as
module.exports.main = (event, context, callback) => {
console.log(event.requestContext.authorizer.claims)
}
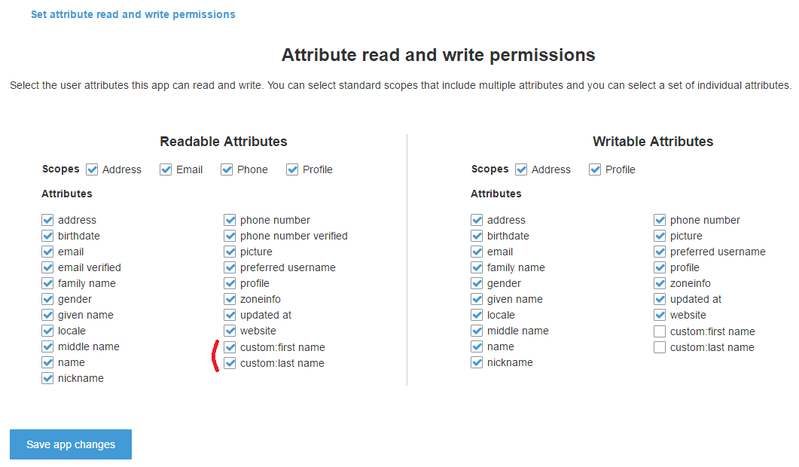
But if you use some custom attributes they will not be included in token by default so you will not be able to get them. To fix this go to your app setting and set attributes you want to include as readable:
So now it should be added in serverless config claims (on in your cloudformation template, or clicked in AWS console) as:
claims:
- email
- nickname
- custom:last_name
- custom:first_name
And when you will test it, don't forget to re-login (or refresh token) because ID token should be regenerated to include new claims!
